Quick Summary
Modern aviation faces four major cybersecurity threats: ransomware attacks on airport operations systems, GPS/GNSS spoofing of aircraft navigation, systemic risk from shared vendor dependencies, and unencrypted legacy communication protocols like ACARS. These threats have evolved beyond data theft to directly disrupting flight operations and passenger safety.

What Is Aviation Cybersecurity and Why Does It Matter?
Aviation cybersecurity refers to the protection of digital systems that support air travel, including check-in platforms, navigation satellites, air traffic communications, and operational technology at airports. Unlike traditional airport security, which focuses on physical threats, aviation cybersecurity defends the invisible digital infrastructure that modern aviation depends on.
The threat landscape has fundamentally shifted. Attacks are no longer primarily aimed at stealing passenger data or frequent flyer miles. The new objective is disrupting operational availability: grounding flights, overwhelming airport staff, and causing cascading delays that affect thousands of travellers.
Threat 1: Ransomware Attacks on Flight Operations
What happened?
In September 2025, a ransomware attack targeted Collins Aerospace’s ARINC MUSE platform, a passenger services system used by multiple European airports. The attack forced affected airports to revert to manual check-in and boarding procedures, causing significant cascading delays for thousands of passengers.
Why is this significant?
Airport operational systems fall into two critical categories:
- Passenger Services Systems — control check-in desks and ticketing
- Operational Technology (OT) — manages boarding gates and terminal passenger flow
A successful attack on either category creates a dual crisis: a technical system failure and a human crisis, as overwhelmed staff attempt to manually process thousands of stranded passengers. The combination amplifies disruption far beyond what either failure would cause alone.
What does this mean for travellers?
A single cyberattack on a widely-used airport platform can simultaneously ground operations across multiple airports in different countries, not because each was individually targeted, but because they all rely on the same software.
Threat 2: GPS Spoofing of Aircraft Navigation
What is GNSS spoofing?
Aircraft rely on Global Navigation Satellite Systems (GNSS) — including GPS — for positioning and navigation. GNSS interference takes two forms:
- Jamming — blocks the satellite signal entirely; flight crews can usually detect this
- Spoofing — broadcasts false satellite signals that feed incorrect but plausible position data to the aircraft’s systems
Spoofing is significantly more dangerous than jamming because aircraft instruments appear to function normally while actively receiving false positional data.
Where is this happening?
Since 2023, GNSS interference incidents have increased sharply, with identified hotspots in:
- Eastern Europe
- The Middle East
- The Eastern Mediterranean
In May 2024, authorities at Seoul Gimpo Airport warned operators to disable GPS inputs due to repeated interference events.
How are regulators responding?
Both the European Union Aviation Safety Agency (EASA) and the US Federal Aviation Administration (FAA) have issued safety bulletins warning operators of ongoing GNSS attacks and providing guidance on detecting and mitigating navigation manipulation.
The long-term solution is Galileo’s Open Service Navigation Message Authentication (OSNMA), which entered initial operational service in July 2025. OSNMA is specifically designed to allow aircraft to verify that navigation signals are genuine.
Threat 3: Single Points of Failure Across the Aviation Industry
What is the shared vendor risk problem?
The global aviation industry relies heavily on a small number of shared technology providers for critical systems. This creates a single point of failure dynamic: one successful attack on a widely-used vendor can simultaneously disrupt airlines and airports across the world.
What are the key examples?
SITA data breach (2021): SITA, a major aviation IT provider, suffered a data breach that exposed passenger and frequent flyer data from multiple major international airlines — all because those carriers used the same SITA system.
ARINC MUSE ransomware attack (2025): The attack on Collins Aerospace’s ARINC MUSE passenger services platform disrupted operations at several European airports simultaneously. Each airport was affected not because it was individually targeted, but because of their shared dependency on a single vendor’s software.
Why is this hard to fix?
Shared platforms exist because they are efficient and cost-effective. However, that same interconnection means a breach propagates instantly across every customer of that platform. Reducing this risk requires either vendor diversification (expensive) or ensuring shared platforms have exceptional security and resilience (challenging to enforce across an industry).
Threat 4: Unencrypted Aircraft Communications (ACARS)
What is ACARS and why is it a security risk?
ACARS (Aircraft Communication Addressing and Reporting System) is the protocol used to transmit short operational messages between aircraft and ground stations. It has been in widespread use for decades.
The critical problem: ACARS operates without encryption or authentication. Messages are transmitted in plaintext, making them:
- Vulnerable to interception by third parties
- Potentially vulnerable to manipulation by sufficiently skilled attackers
Sending sensitive operational data over ACARS has been described as equivalent to writing it on an open postcard.
Is there a better alternative?
ATN/CPDLC (Aeronautical Telecommunications Network / Controller-Pilot Data Link Communications) offers improved security through higher-level protocols. However, its adoption is inconsistent across the global fleet, leaving a patchwork of security standards — with unencrypted ACARS remaining a significant weak link.

How Is the Aviation Industry Responding?
| Threat | Current Response | Status |
|---|---|---|
| Ransomware on operations | Improved cyber resilience plans, manual fallback procedures | Ongoing |
| GNSS spoofing | Galileo OSNMA authentication system | Operational since July 2025 |
| Shared vendor risk | Regulatory scrutiny, resilience planning | Developing |
| ACARS encryption | ATN/CPDLC adoption | Inconsistent / partial |
Frequently Asked Questions
Can a cyberattack actually crash a plane? Current evidence points to disruption of operations and navigation reliability rather than direct control of aircraft. However, GNSS spoofing poses a genuine safety risk by feeding false positional data to navigation systems, and the concern is taken seriously enough that EASA and the FAA have issued formal safety bulletins.
What is the most dangerous aviation cybersecurity threat right now? GNSS spoofing is widely considered the most acute safety risk because it directly affects navigation and is difficult for flight crews to detect in real time. Ransomware on airport operations is the most disruptive threat in terms of passenger impact.
What is OSNMA? OSNMA (Open Service Navigation Message Authentication) is a Galileo satellite system feature that allows receivers to cryptographically verify that navigation signals are genuine and have not been spoofed. It entered initial operational service in July 2025.
Are airports prepared for cyberattacks? Preparedness varies. The 2025 ARINC MUSE attack demonstrated that even widely-used enterprise systems can be vulnerable. Airports are developing improved cyber resilience plans, including procedures to maintain operations during IT outages — but the industry acknowledges that modernising legacy systems remains a significant challenge.
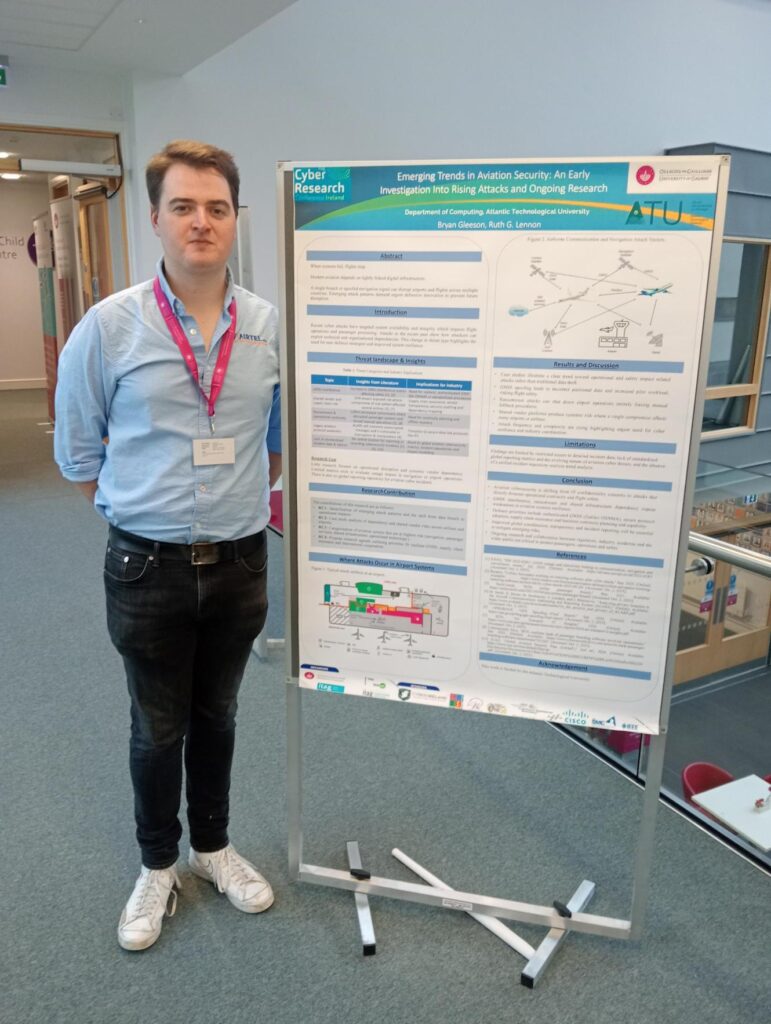
This article was written and researched by Airtel team Member Bryan Gleeson for TU.